
Panda Adaptive Defense
Find the Answer, Solve the Problem
Panda Security is now a part of WatchGuard Technologies, please visit our WatchGuard Technologies website to learn more about this product!
Overview:
Panda's endpoint detection and response (EDR) service is the best cyber-security solution to protect your business against targeted attacks and advanced persistent threats.
Adaptive Defense protects every endpoint, server, laptop and road warrior on your corporate network, detecting and blocking the malware and unusual behavior that other products on the market are unable to stop.

The malware and IT security panorama has undergone a major change in terms of volume and sophistication. There has been an exponential increase in the number of viruses in circulation (around 200,000 new viruses appear every day), and new techniques for penetrating defenses and hiding malware are allowing threats to remain on corporate networks for long periods.
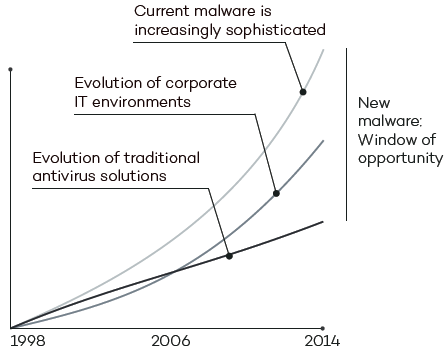
At the same time, IT environments have become increasingly complex, making management more difficult and systems more vulnerable.
Yet traditional antivirus solutions are out of step with the reality. Their linear evolution continues to use outdated detection techniques based on signature files and heuristic algorithms. This means that the results are inaccurate, i.e., that malware can go undetected and false positives are generated.
This discrepancy has led to what has been dubbed the 'window of opportunity for malware': the time lapse between the appearance of a new virus and the release of the antidote by security companies. An increasing gap that is exploited by hackers to get viruses, ransomware, Trojans and other types of malware into corporate networks. Such increasingly common threats can encrypt confidential documents and demand a ransom, or simply collect sensitive data for industrial espionage.
Governments, banks and other large companies are bearing the brunt of attacks that traditional antivirus solutions are simply not detecting in time. Our Research Department has analyzed millions of virus samples and the best antivirus products on the market to reveal that 18 percent of malware is undetected in the first 24 hours after it is released, and even after three months, these traditional solutions are still unable to detect 2 percent of malware.
The solution to this situation is Adaptive Defense: a Panda Security service which can accurately classify every application running in your organization, only allowing legitimate programs to run.
To achieve this, we have been working for five years on a new security model based on three principles: continuous monitoring of applications on a company's computers and servers, automatic classification using machine learning on our Big Data platform in the cloud, and finally, our technical experts analyze those applications that haven't been classified automatically to be certain of the behavior of everything that is run on the company's systems.
Why do you need Adaptive Defense if you already have an antivirus in your company?
The volume of malware has increased exponentially and attacks have become far more sophisticated.
This new trend, combined with the increasing complexity of IT environments, is allowing hackers to access companies and leave malware which then remains hidden for long periods.
Traditional antivirus solutions are efficient against commodity malware, but they fail to prevent the new generation of advanced threats and targeted attacks.
Adaptive Defense is an endpoint detection and response (EDR) service that can accurately classify every process running in an organization, only allowing legitimate programs to run.
The new technology included in Adaptive Defense will allow you to protect your business against targeted and zero-day attacks which exploit the time lapse between the appearance of a new virus and its neutralization by security vendors.
We've made prevention the best defense against targeted attacks
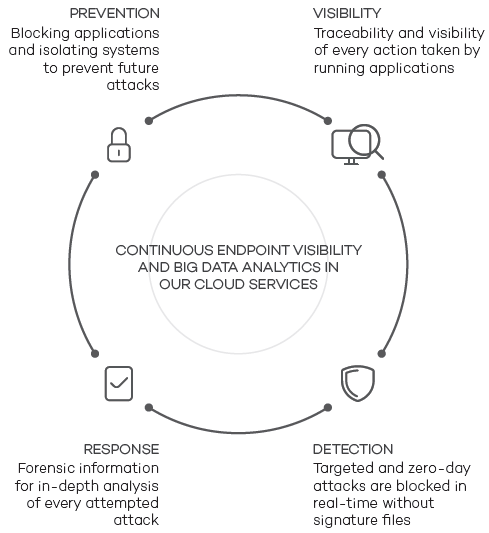
Visibility
Get complete visibility into the applications run on your company's endpoints and servers, as well as every action carried out on your systems.
Detection and Blocking
Detect and block targeted and zero-day attacks in real time before they occur.
Protection and Response Based on Information
Thanks to the forensic reports provided by Adaptive Defense, you will have all the data you need about attacks targeting your systems, allowing you to analyze them and build new security barriers for your IT environment.
Attack Prevention
Block any applications that are not considered goodware, isolating your company from future attacks.
Features:
Protection and Disinfection
Basic and extended blocking
Adaptive Defense provides two types of application blocking to secure your company against any IT attack:
Basic blocking allows applications classified as goodware to run, as well as those that are yet to be cataloged by Panda Security's automated systems and malware experts.
Extended blocking only permits the execution of applications classified as goodware. This is the ideal form of protection for companies with a ‘zero risk’ approach to security.
Protection for vulnerable systems
Endpoints and servers with operating systems that are not updated will no longer be a problem for the integrity of your IT security.
Adaptive Defense offers protection for vulnerable systems with operating systems no longer supported by the vendor, such as Windows XP, without the need to install a traditional antivirus.

No false positives thanks to big data and the cloud
Adaptive Defense monitors all the actions that occur as a consequence of the running of any application on your company’s workstations and servers.
This monitoring process, in conjunction with Machine Learning on Big Data platforms in the cloud, enables us to identify and classify the behavior of every application.
Panda Security experts also analyze any applications that are not classified automatically in order to obtain detailed knowledge of the processes being run in your organization.
In short, you can decide at any time which applications are run in your company. Adaptive Defense will give you the peace of mind that any application run in your organization is 100% safe for the security of your environment. Always, and without false positives.
 Service Management
Service Management
100% Managed Service
Panda Security’s latest technologies based on Machine Learning and Big Data environments give Adaptive Defense the ability to automatically classify applications without end-user intervention.
Zero impact on customers' infrastructure
The service is managed entirely from acentralized Web console which lets you manage the security of your Windows workstations, servers, smartphones and remote offices.
Control and Diagnostics of IT Resources
Forensic Reports
Adaptive Defense provides forensic reports and execution graphs that give you a clear view of all the events caused by malware.
You can trace the path of any attack before it was neutralized, as well as the files created and much more with heat maps available through the Web console. Identify the critical vulnerabilities in your organization and fix them.
Continuous Network Status Information
Adaptive Defense sends immediate alerts when malware is detected on the network.
Additionally, the service's reports provide in-depth information about the location of threats, the computers infected and the actions taken by the malware.
These reports can also be sent via email and include details of the daily activity of the service.
SIEM Integration
Our service integrates with SIEM products such as QRadar or ArcSight, aggregating detailed information on the activity of all applications run on company systems
The information about security events stored on the system will let you analyze in real time behavior patterns of your employees and network trends.
For those without SIEM, Adaptive Defense optionally includes its own security event management and storage system for real-time analysis of all the collected data.
Benefits:

Complete and Robust Protection Guaranteed
Panda Adaptive Defense offers two operational modes:
- Standard mode allows all applications cataloged as goodware to be run, along with the applications that are yet to be cataloged by Panda Security and the automated systems.
- Extended mode only allows the running of goodware. This is the ideal form of protection for companies with a 'zerorisk' approach to security.

Forensic Information
- Execution event graphs give a clear view of all events caused by malware.
- Get visual information through heat maps on the geographical source of malware connections, files created and much more.
- Locate software with known vulnerabilities installed on your network.

Compatible with Traditional Antivirus Solutions
Adaptive Defense can coexist with traditional antivirus solutions, and take the role of a corporate tool capable of blocking all types of malware, including targeted and zeroday attacks that such traditional solutions are unable to detect.

Protection for Vulnerable Operating Systems and Applications
Systems such as Windows XP, which are no longer supported by the developer and are therefore unpatched and vulnerable, become easy prey for zero-day and new generation attacks.
Moreover, vulnerabilities in applications such as Java, Adobe, Microsoft Office and browsers are exploited by 90% of malware.
The vulnerability protection module in Adaptive Defense uses contextual and behavioral rules to ensure companies can work in a secure environment even if they have systems that are not updated.

Continuous Information on Network Status
- Get immediate alerts the moment that malware is identified on the network, with a comprehensive report detailing the location, the computers infected, and the action taken by the malware.
- Receive reports via email on the daily activity of the service.

SIEM Available
Adaptive Defense integrates with SIEM solutions to provide detailed data on the activity of all applications run on your systems.
For clients without SIEM, Adaptive Defense includes its own system for storing and managing security events to analyze all the information collected in real-time.

100% Managed Service
Forget about having to invest in technical personnel to deal with quarantine or suspicious files or disinfect and restore infected computers. Adaptive Defense classifies all applications automatically thanks to machine learning in our big data environments under the continuous supervision of PandaLabs' experts.
Technical Requirements:
| Technical Requirements | |
|---|---|
| Web Console (only monitoring) |
|
| Agent |
|
Compare:
| Adaptive Defense 360 | Adaptive Defense | Endpoint Protection | Endpoint Protection Plus | Systems Management | Fusion | Fusion 360 | |
|---|---|---|---|---|---|---|---|
| Protection | |||||||
| Protection against known and zero-day malware | |||||||
| Protection against known and zero-day ransomware | |||||||
| Protection against known and zero-day exploits | |||||||
| Anti-spyware, anti-phishing protection, etc. | |||||||
| Protection for multiple attack vectors (Web, email, network, devices) | |||||||
| Traditional protection with generic and optimized signatures | |||||||
| Protection against Advanced Persistent Threats (APT) | |||||||
| Managed service: Classification of 100% of applications before execution (1*) | |||||||
| Managed service: Threat Hunting (2*) | |||||||
| Queries to Panda’s cloud-based collective intelligence | |||||||
| Behavioral blocking and IoA detection | |||||||
| Personal and managed firewall | |||||||
| IDS / HIDS | |||||||
| Ability to block unknown and unwanted applications | |||||||
| Device control | |||||||
| URL filtering by category (Web browsing monitoring) | |||||||
| Content, Virus and Spam filtering for Exchange Server | |||||||
| Built-in antivirus protection for Exchange Server | |||||||
| Built-in anti-spam protection for Exchange Server | |||||||
| Monitoring | |||||||
| Advanced endpoint security | |||||||
| Cloud-based continuous monitoring of all process activity | |||||||
| Data retention for one year for retrospective attack investigation | |||||||
| Detection | |||||||
| Detection of compromised trusted applications | |||||||
| Managed service: Classification of 100% of applications during and after execution (1*) | |||||||
| Fully configurable and instant security risk alerts | |||||||
| Containment | |||||||
| Real-time computer isolation from the cloud console | |||||||
| Response and remediation | |||||||
| Ability to roll back and remediate the actions committed by attackers | |||||||
| Centralized quarantine | |||||||
| Automatic analysis and disinfection | |||||||
| Investigation | |||||||
| Managed service: Threat Hunting (2*) | |||||||
| Incident graphs and lifecycle information available from the Web console | |||||||
| Ability to export lifecycle information for local analysis | |||||||
| Advanced Visualization Tool (add-on) | |||||||
| Discovery and monitoring of unstructured personal data across endpoints (add-on) | |||||||
| Attack surface reduction | |||||||
| Information about each computer's hardware and software components | |||||||
| Information about the Microsoft updates installed on endpoints | |||||||
| Real-time information about the status of all protections and communications | |||||||
| Unattended, automatic updates | |||||||
| Automatic discovery of unprotected endpoints | |||||||
| Ability to immediately protect unprotected endpoints remotely | |||||||
| Panda native proxy to support endpoints with no Internet connection | |||||||
| Endpoint security management | |||||||
| Centralized cloud-based console | |||||||
| Settings inheritance between groups and endpoints | |||||||
| Ability to configure and apply settings on a group basis | |||||||
| Ability to configure and apply settings on a per-endpoint basis | |||||||
| Real-time deployment of settings from the console to endpoints | |||||||
| Security management based on endpoint views and dynamic filters | |||||||
| Ability to schedule and perform tasks on endpoint views | |||||||
| Ability to assign preconfigured roles to console users | |||||||
| Ability to assign custom permissions to console users | |||||||
| User activity auditing | |||||||
| Installation via MSI packages, download URLs, and emails sent to end users | |||||||
| On-demand and scheduled reports at different levels and with multiple granularity options | |||||||
| Security KPIs and management dashboards | |||||||
| System status reports at different levels and with multiple granularity options | |||||||
| Device inventory and audits | |||||||
| Agent and agentless monitoring of devices | |||||||
| Patch management | |||||||
| Centralized software installation | |||||||
| Non-disruptive remote access | |||||||
| Remote Desktop | |||||||
| Built-in chat | |||||||
| Task automation and scripting | |||||||
| Component store - ComStore | |||||||
| Ticketing/Help Desk | |||||||
| Modules | |||||||
| Panda Data Control integration | |||||||
| Advanced Reporting Tool integration | |||||||
| SIEM integration | |||||||
| Panda Patch Management | |||||||
| Panda Full Encryption inregration | |||||||
| High availability service | |||||||
| Host platform certifications | ISO27001, SAS 70 ISO27001, SAS 70 | ISO27001, FISMA, SAS70, PCI DSS | |||||
| Supported operating systems | |||||||
| Supports Windows | |||||||
| Suppots Exchange | |||||||
| Supports macOS X | |||||||
| Supports Linux | |||||||
| Supports Android | |||||||
| Supports iOS | |||||||
| Support for virtual environments - persistent and non-persistent (VDI)** | |||||||
* Panda Fusion is a bundle of Panda Endpoint Protection Plus and Panda Systems Management. Panda Fusion 360 is the combination of Panda Systems Management and Panda Adaptive Defense 360 that are sold separately
** Compatible systems with the following types of virtual machines: VMWare Desktop, VMware Server, VMware ESX, VMware ESXi, Citrix XenDesktop, XenApp, XenServer, MS Virtual Desktop y MS Virtual Servers. Panda Adaptive Defense 360 & Panda Fusion 360 solutions are compatible with Citrix Virtual Apps, Citrix Desktops 1906 & Citrix Workspace App for Windows, Panda Securtity has been verified as Citrix Ready partner.
1* 100% Classification Service.
2* Threat Hunting and Investigation Service
Documentation:
Download the Panda Adaptive Defense Datasheet (.PDF)

